A historically accurate simulation of the famous Enigma cipher machine used in the Second World War.
The app is available exclusively on F-Droid.

Historically Accurate Enigma Models
- Model I (Heer, Luftwaffe)
- Model M3 (Heer, Marine)
- Model M4 (“Shark”, Marine)
- Model G31/A865 (Abwehr)
- Model G312 (Abwehr)
- Model G260 (Abwehr)
- Model D (commercially used)
- Model K
- Model Swiss-K (Swiss)
- Model Swiss-K (Swiss, Luftwaffe)
- Model KD
- Model R (“Rocket”, Reichsbahn)
- Model T (“Tirpiz”, Japan)
The mechanics of the Enigma have been reverse-engineered from Wikipedia articles and other documents.
All models can be used with their historical setup. That includes up to 5 rotors (“Walzen”) which contain different wiring depending on the model, a plugboard (“Steckbrett”) to add further scrambling to the Enigma’s wiring, as well as a different settings for the ring around the rotors (“Ringstellung”).
The app supports exporting the machines settings to a code, which can be shared to quickly restore the same settings on another device. Messages can quickly be encrypted by sharing them to the app.
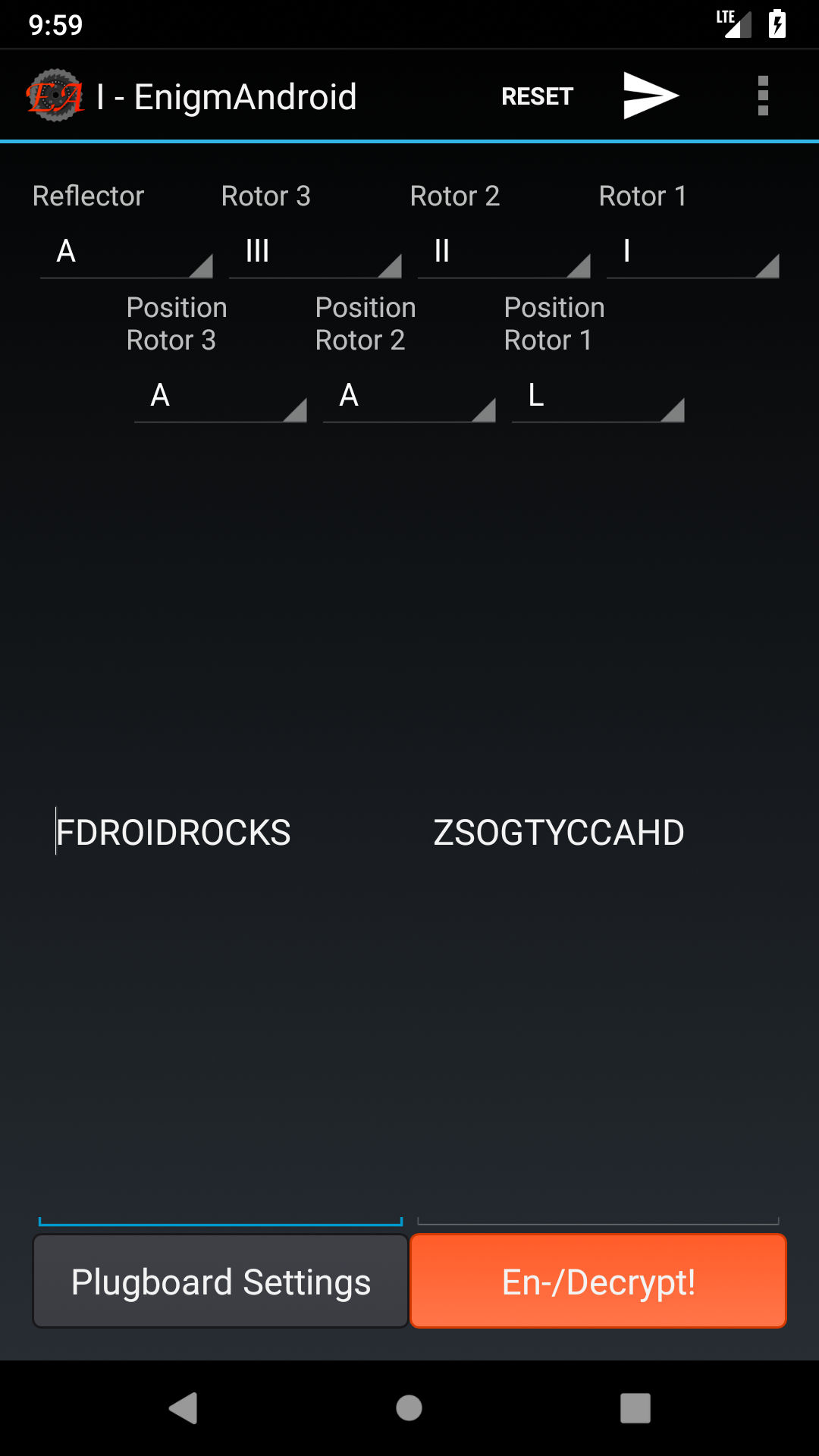
Main interface of the Simulator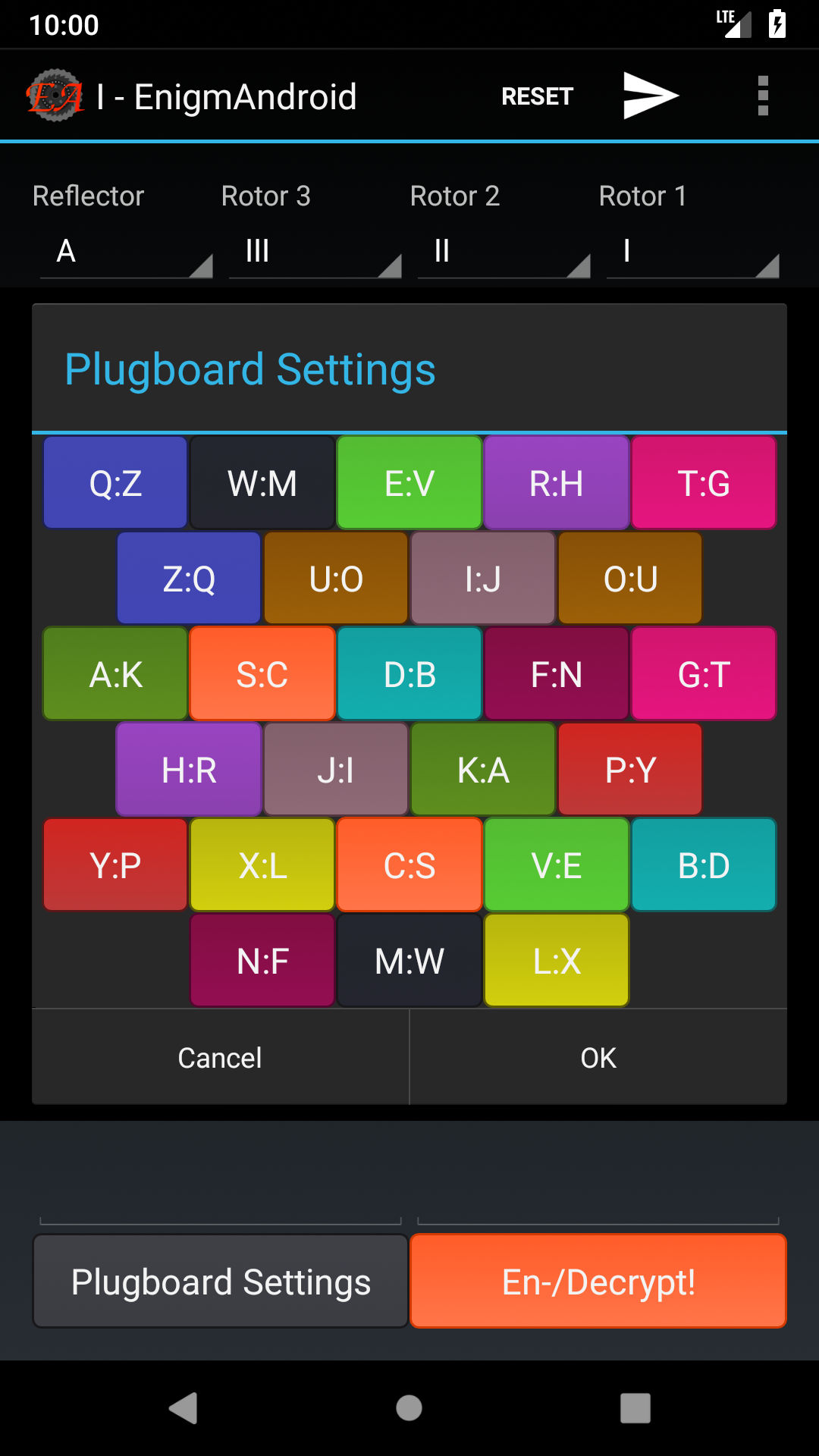
The customizable Plugboard (Steckerbrett) 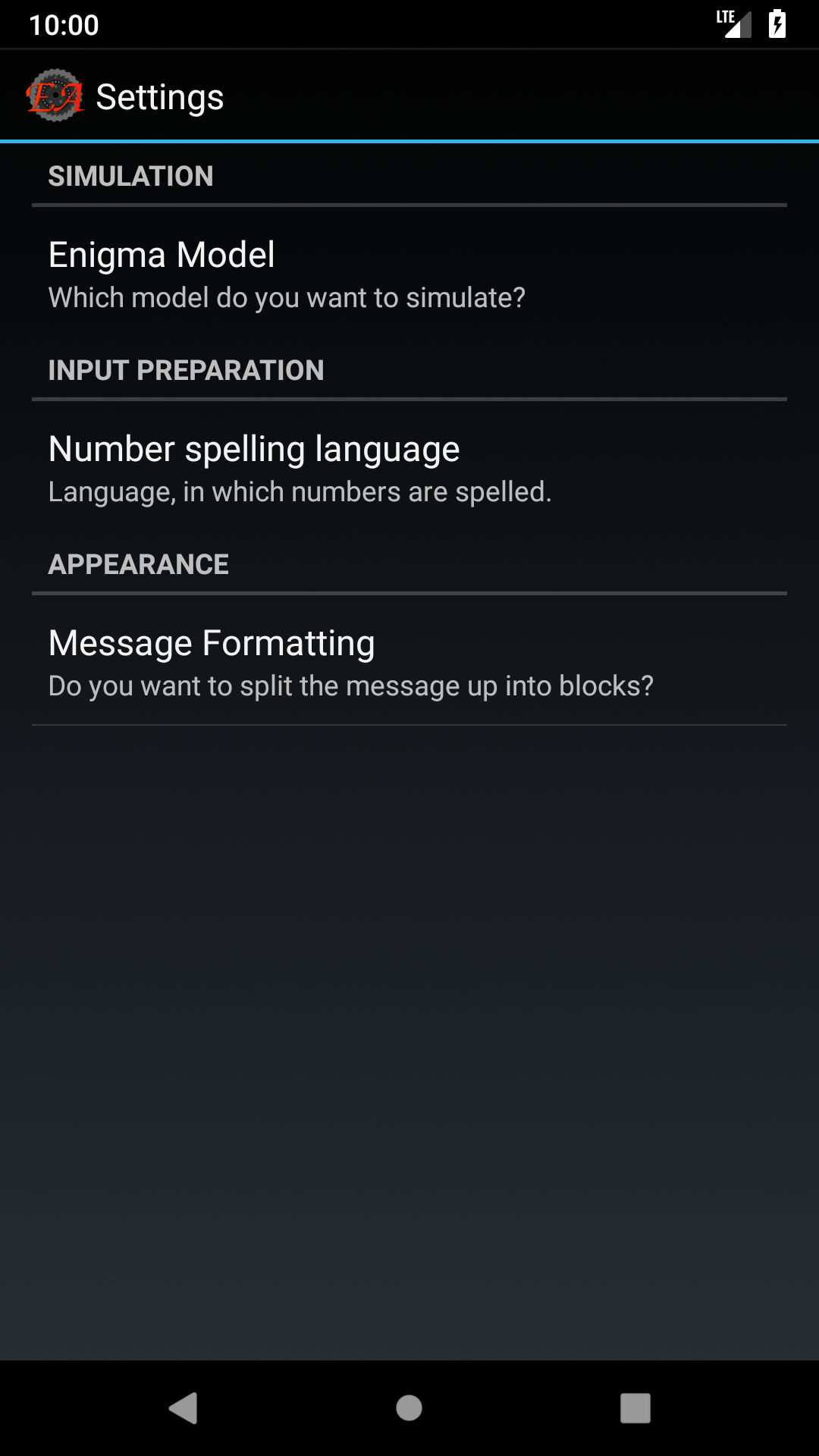
The Settings Screen 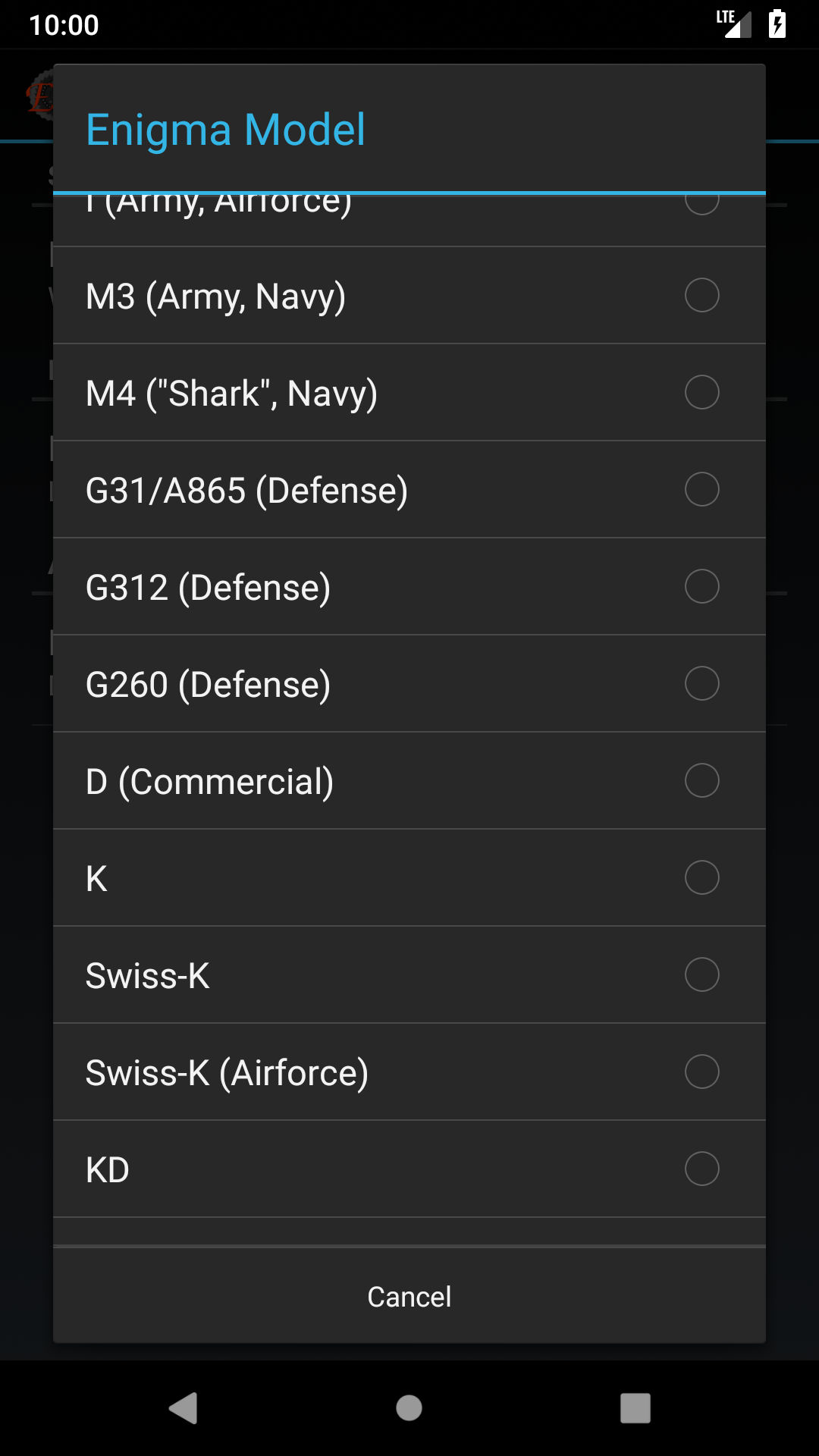
Wide variety of accurate historic Enigma Models
The source code of the app is licensed under the GNU GPLv3+ and is available on Github, as well as on Codeberg.org.
Historical Background
The Enigma cipher machine was used by Nazi Germany in World War II to send and receive encrypted messages.