-
Unified Encrypted Payload Elements for XMPP
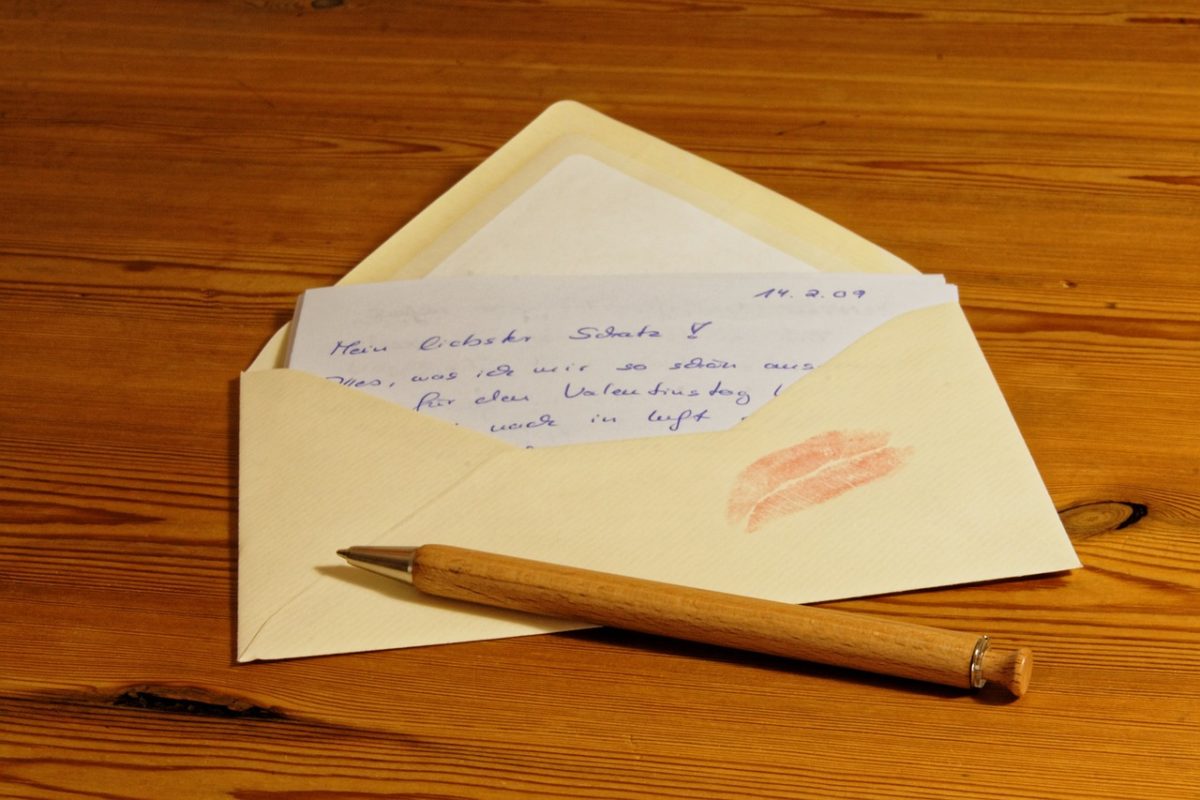
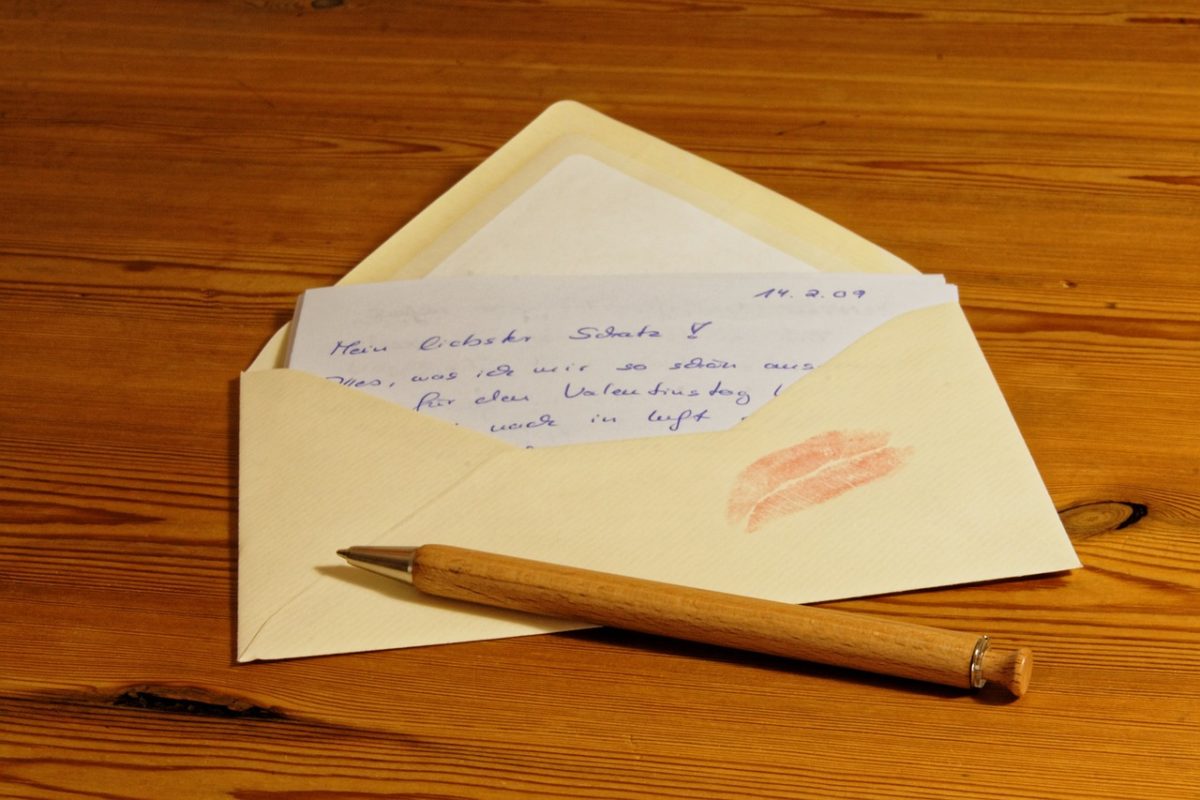
An envelope hiding the original message – Image by Bru-nO This is a proposal to extract the element encryption principle from OpenPGP for XMPP to make it applicable to other encryption protocols.
This is a proposal to extract the element encryption principle from OpenPGP for XMPP to make it applicable to other encryption protocols.