This is the project page for my Summer of Code project 2018. As you can read in the title, my project is about an implementation of OpenPGP for XMPP (short: OX) in the XMPP client library Smack.
OpenPGP for XMPP is specified in XEP-0373 and XEP-0374, where 373 specifies general building blocks, while the latter describes the usage profile for instant messaging (OX-IM).
Smack: smack-openpgp
The major part of my GSoC project is an OX:IM implementation for the XMPP client library Smack. This was done as the Smack module smack-openpgp, which contains an implementation of XEP-0373 and XEP-0374. It consists of XMPP extension elements and providers, as well as manager classes which handle the OX workflow.
I designed an easy to use API, which gives client developers the oportunity to quickly implement OpenPGP encrypted instant messaging. My implementation is capable of public key exchange over PubSub, encrypted secret key exchange between the users devices, as well as general encrypted messaging with signature verification. The user also has the option to easily generate fresh OpenPGP keys (RSA, ElGamal, EC) through PGPainless.
During the project, I created a bunch of JUnit and Integration tests to ensure correct functionality.
My code has already been merged into Smacks master branch and can be found in the smack-openpgp module.
PGPainless
The second big part of my project is PGPainless.

PGPainless is my library for OpenPGP. It started as a fork of Jens Neuhalfens bouncy-gpg, but I quickly decided to start from scratch and write my own library. This quickly grew into a standalone project (https://pgpainless.org), which I will thrive to extend further. As I understand, there is a need for easy to use OpenPGP libraries for Java and Android. In fact, Android compatibility was one of the reasons to start from scratch instead of going with existing implementations.
PGPainless is based around Bouncycastle, but it provides an easy to use API, which allows to execute cryptographic actions without touching any bouncycastle code at all. The plan is to make pgpainless as easy to use as possible, so that it can be incorporated in other (also non-Smack) projects that want to implement OpenPGP for XMPP (and other purposes as well).
Demo client
I created a small command line client which demonstrates the capabilities of my OpenPGP API for Smack. It is able to generate user keys, restore existing secret key backups from pubsub, and obviously exchange encrypted messages with other users.
You can find it here. Enjoy testing 🙂
Contributions to other projects
During my work, I…
- detected a bug in Bouncycastle which caused exported keys to have an invalid format by using a wrong checksum in unencrypted keys.
- detected another bug in Bouncycastle, which caused exported sub-keys to have a wrong package format, causing them to get lost on import.
- created a small patch for an inconvenience in Bouncycastle.
- Gave feedback and did some formal work on XEP-0373 and XEP-0374 ([1], [2], [3], [4], [5], [6]).
- Tested my implementation against another experimental OX application and gave feedback.
Blog Highlights
Throughout the whole GSoC period, I blogged extensively about my progress.
- Another Summer of Code with Smack
- Summer of Code: Preparations
- Summer of Code: The plan. Act 1: OpenPGP
- Summer of Code: Small steps
- Summer of Code: The Plan. Act 1: OpenPGP, Part Two
- Summer of Code: Quick Update
- Summer of Code: Bug found!
- Summer of Code: Advancing the prototype
- Summer of Code: Polishing the API
- Summer of Code: Command Line OX Client!
- Summer of Code: PGPainless 2.0
- Summer of Code: Evaluation and Key Lengths
- Summer of Code: The demotivating week
- Summer of Code: An (almost) three line fix to a three days problem
- Summer of Code: Checkstyle to the rescue!
- Summer of Code: Second evaluation phase
- Summer of Code: Plan for the grand finale
- Summer of Code: First PGPainless Release!
- Summer of Code: Finalizing the PR
- Summer of Code: Smack has OpenPGP Support!
One of my personal favourites is my posting from May 17th, in which I explained a bug in Bouncycastle, that I found.
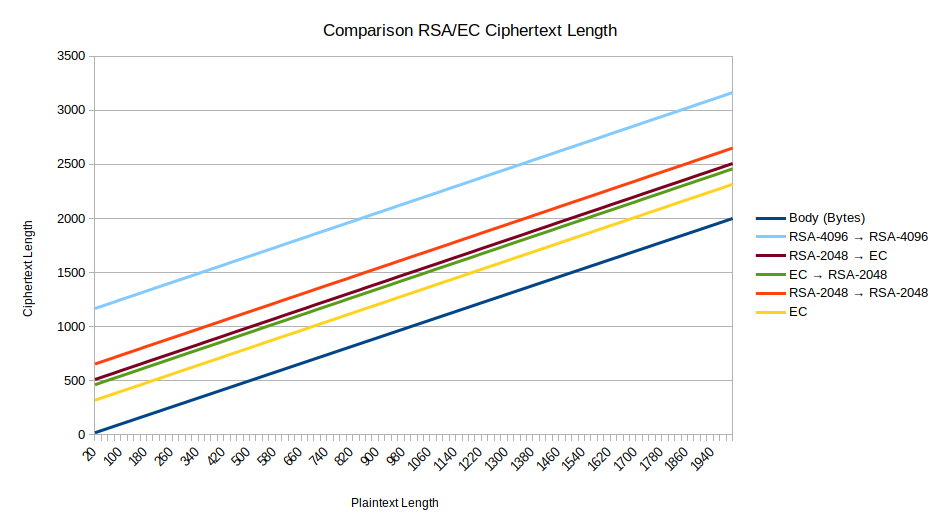
I’m also proud of my posting from June 11, in which I investigated OpenPGP message lengths depending on which key types are used.


